Industrial Control Systems (ICS) - including PLCs, SCADA, HMIs, drives, instrumentation networks, and the control panels that bring them together - are designed for stability and uptime. Historically, many were engineered to be reliable and serviceable, not secure by modern cyber standards. That gap is now a board-level risk because cyber incidents in operational technology (OT) can cause real-world consequences: unexpected shutdowns, loss of temperature control, damaged equipment, safety events, and extended downtime. These incidents directly threaten production continuity and real world operations in industrial settings, as the risks are not just digital but also impact physical processes and the uptime of critical infrastructure.
At the same time, the regulatory landscape is tightening. Across the UK and EU, cyber resilience expectations are being pushed into critical infrastructure, manufacturing, and products placed on the market. For many industrial sites, 2026/27 is the period when cyber security moves from “best practice” to “compliance pressure” - and when audit questions start to shift from IT-only controls to OT reality.
💡 Key Insight: In OT, cyber security is not only a data problem. It is an uptime, safety, and engineering integrity problem.
What is an Industrial Control System (and what counts as “OT”)?
An ICS is the combination of equipment and software used to monitor and control industrial processes in various industrial environments. ICS systems and OT systems are deployed to ensure operational safety, efficiency, and reliability. Management systems, such as building management systems and energy management systems, are used to optimise and monitor building and energy operations.
In practical terms, OT typically includes:
PLCs (programmable logic controllers) and remote I/O (including safety PLCs where fitted), which are physical components used for automation and control in industrial environments
SCADA platforms, historians, alarm servers, and engineering workstations
HMIs, touch panels, operator stations, local displays
Industrial networks (Ethernet/IP, Profinet, Modbus TCP/RTU, etc.)
Drives, soft starters, intelligent motor control, MCC interfaces
Instrumentation and measurement networks
Control panels, power supplies, network switches, remote access devices
Building management systems, energy management systems, and distributed control systems as examples of integrated management systems for facility and process optimisation
Many sites also have “hybrid” assets that sit between IT and OT - for example, remote monitoring gateways, cloud dashboards, production reporting systems, and vendor-managed service connections. These can add value, but they also expand your attack surface if not engineered correctly.
Definition: Attack surface is the total number of pathways an attacker could use to access systems - including network links, remote access methods, shared credentials, exposed services, and insecure devices.
Why ICS cyber risk is different from IT cyber risk
A common mistake is applying IT security assumptions directly to OT. The goals overlap - reduce risk and prevent compromise - but OT constraints are different. OT environments often prioritise continuous operation, predictable timing, and stable change control.
ICS environments also contain legacy components and protocols that were never designed with security in mind. Many of these are legacy systems that rely on outdated operating systems and outdated protocols, which lack modern cybersecurity features such as encryption and authentication.
Many ICS environments operate with existing legacy technologies and proprietary protocols due to their original design priorities, which focused on operability and reliability rather than cybersecurity.
⚠ OT reality: In many plants, the fastest way to create downtime is to apply “security” changes without understanding control dependencies, interlocks, and recovery sequences.
What risks does this issue create?
ICS cybersecurity risks can be grouped into four operational outcomes. Each one has a direct relationship with uptime and compliance. Cyberattacks can cause operational disruption to critical systems and vital systems, impacting production processes and industrial production. This can result in halted manufacturing, safety risks, and significant losses for industrial organisations.
1) Loss of control and unplanned shutdown
If an attacker (or even a well-intentioned user with the wrong access) can modify logic, change setpoints, or interrupt communications, the plant can lose supervisory control over critical physical processes, leading to unplanned shutdowns. This could be immediate (e.g., drive stop commands, PLC mode change) or delayed (e.g., subtle setpoint drift that triggers process instability later).
Compromised industrial control systems can also pose serious physical safety risks to employees and the public, as cyberattacks may damage equipment or endanger lives by disrupting the safe operation of physical processes.
2) Loss of visibility and delayed response
Many incidents become major outages because operators lose alarms, trends, or system status. Loss of data acquisition capabilities in SCADA or HMI systems can contribute to loss of visibility and delayed response, as engineers may revert to manual checks and conservative shutdown decisions because they cannot trust what the system is doing.
3) Unsafe or non-compliant operation
In regulated environments (including food and temperature-critical operations), failures in safety systems can lead to unsafe operation and directly threaten human safety. Uncontrolled changes can undermine compliance: incorrect temperature logging, missing alarm evidence, or loss of audit trails. Even if the process continues running, you may not be able to evidence that it ran within specification.
4) Extended recovery time
OT recovery is often slower than IT recovery because systems are coupled to physical equipment. Restoring an image is not enough if you also need to verify logic, alarm handling, interlocks, sequencing, and safe restart conditions.
❗ Risk pattern: The biggest cost is rarely the initial compromise. It is the extended downtime and loss of confidence in control integrity afterwards.
What is changing in 2026/27?
2026/27 is notable because multiple frameworks and regulatory requirements converge around cyber resilience, including expectations on incident reporting, supply chain responsibility, and cybersecurity as part of “essential requirements” for products and machinery.
Industrial organisations must address both existing and new cybersecurity risks as regulatory expectations evolve. The convergence of IT and operational technology (OT) has expanded the attack surface of industrial control systems, increasing cybersecurity risks that must be managed to protect critical infrastructure and ensure operational continuity.
EU: Cyber Resilience Act (CRA) - reporting from September 2026, broad obligations from December 2027
The EU Cyber Resilience Act introduces baseline cyber security requirements for products with digital elements and ties compliance to CE marking. Reporting obligations apply from 11 September 2026, with the main obligations applying from 11 December 2027.
For industrial sites, this matters because control system components - including gateways, industrial networking products, edge devices, and software used in OT - may fall into scope depending on how they are supplied and used. It also changes what “good procurement” looks like: you will increasingly be expected to know what security assurances exist for the products you deploy.
EU: Machinery Regulation (EU) 2023/1230 - applies from January 2027
The EU Machinery Regulation becomes applicable from 20 January 2027. It reflects the reality that digitalisation and “industrial security” now affect machinery safety and compliance.
For organisations that design, integrate, or place machinery on the EU market - or operate equipment supplied under these regimes - cyber security is increasingly linked to safety, conformity assessment, and the integrity of control functions.
EU: NIS2 - already in force, but enforcement maturity continues
NIS2 required Member States to transpose it by 17 October 2024 and applies from 18 October 2024. While this is not a 2026/27 date, many organisations are only now experiencing the practical impact as national implementations mature.
UK: Cyber Security and Resilience (Network and Information Systems) Bill - enforcement expected across 2026/27
The UK government introduced a Cyber Security and Resilience Bill in November 2025 to expand and strengthen the UK’s NIS-style regime, including broader scope and tighter incident reporting expectations. Official government materials outline its intent to update the framework.
Public reporting and commentary indicates the UK’s approach is expected to develop through secondary legislation and phased implementation across 2026 and 2027.
ℹ Practical takeaway: Even if your site is not “formally in scope” today, customer audits, insurer questions, and supply chain requirements often move faster than legislation. Treat 2026/27 as the point where OT cyber resilience becomes an expected engineering baseline.
How compliance affects ICS cyber security in real terms
Compliance pressure changes behaviour in three ways: it formalises accountability, it demands evidence, and it raises the cost of weak controls. For OT, the evidence requirement is often the hardest part because many plants cannot currently demonstrate what they have, how it is configured, or how access is controlled.
In practical terms, compliance expectations tend to focus on:
Governance - who owns OT cyber risk and how decisions are controlled
Asset knowledge - accurate inventories of PLCs, HMIs, network devices, remote connections. A comprehensive asset inventory is foundational for ICS security, as you can't protect what you can't see.
Access control - who can change logic, who can connect remotely, how credentials are managed. It is essential to enforce access controls, implement access management, and follow ICS security best practices such as least privilege, strong passwords, and multi-factor authentication.
Incident readiness - detection, response, containment, and recovery planning
Supply chain assurance - understanding vendor access, product security posture, and update responsibilities
Security assessments - evaluating third-party vendors and supply chain risks to identify vulnerabilities and ensure compliance with security standards
Security practices - implementing effective security measures and risk management strategies to safeguard OT environments
Audit-ready OT evidence pack (minimum expectation)
✅ OT asset register (PLCs, HMIs, SCADA servers, switches, gateways)
✅ Network segmentation diagram (what is separated from what, and how)
✅ Remote access inventory (methods, owners, MFA status, vendor accounts)
✅ Backup and restore proof (logic backups, images, restore test evidence)
✅ Change control records for PLC/SCADA modifications
✅ Incident response playbook for OT (including safe shutdown and restart)
Engineering considerations: the OT controls that actually reduce downtime risk
The goal is not to turn a plant into an IT environment. The goal is to implement controls that reduce the likelihood and impact of compromise without destabilising operations. Security teams play a crucial role in implementing and continuously monitoring these controls, ensuring real-time visibility into industrial control systems and enabling faster response to potential threats.
1) Network segmentation and controlled pathways
If your PLC network is flat, anything that gains access can “see” everything. Effective network segmentation is crucial in industrial automation cybersecurity to limit threat movement across systems and protect the ICS network. Segmentation reduces blast radius. It also makes maintenance safer because changes can be isolated.
A practical approach is to separate at least: business IT, plant supervision (SCADA/historians), control networks (PLC/I/O), and safety or critical monitoring, where applicable. Then define and document the allowed pathways between zones.
Segmentation rule of thumb
If a device does not need to talk to another device to support the process, it should not be able to - not by policy, but by design.
2) Secure remote access (vendor access included)
Remote access is one of the highest-risk areas in OT, especially where multiple vendors maintain equipment. The objective is not “no remote access”, but “remote access that is controlled, logged, and revocable”.
Practical measures include: time-bound access, named accounts (no shared vendor logins), multi-factor authentication where feasible, approval workflows, session logging, and a clear offboarding process when contracts change. Critically, remote access should land in a controlled zone, not directly onto the PLC network.
⚠ Common weakness: Remote access installed for convenience becomes permanent infrastructure - but without ownership, documentation, or evidence of who used it and when.
3) Backup, restore, and “known-good” control integrity
OT backups are not only about disaster recovery. They are about proving control integrity. If you cannot restore PLC logic confidently, you cannot recover quickly. A robust approach includes: versioned PLC programs, SCADA configurations, HMI projects, key device parameters, and images for critical servers or engineering workstations.
Equally important is restoration testing. Many organisations have backups that look correct until they are needed. A restore test - planned, evidenced, and repeated - is one of the most uptime-protective controls you can implement.
❗ Uptime truth: The only backup that matters is the one you have successfully restored.
4) Patch and vulnerability management that respects uptime
OT patching must be risk-based, and effective patch management is a critical security control for industrial control systems. Not every device can be patched quickly, and some patches can introduce stability issues. Patching strategies should prioritize systems by their exploitability and the impact of their downtime.
For sites operating 24/7, a planned maintenance window strategy is often necessary. Where patching is impossible, document the rationale and the compensating controls - that documentation often becomes crucial in audits and insurer discussions.
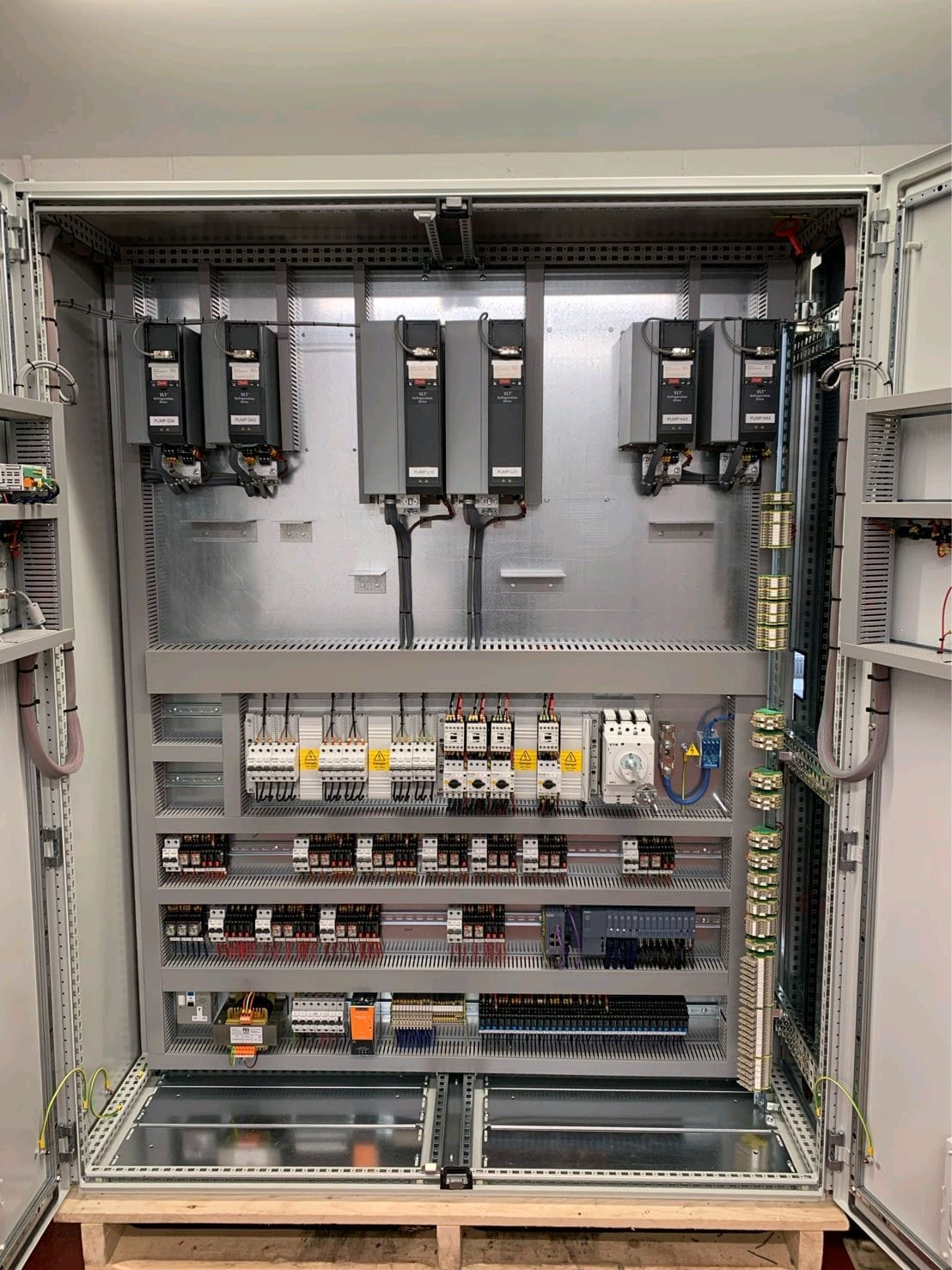
5) Control panels and physical security still matter
Cyber risk in OT is not purely “network”. Control panels often contain network switches, remote access devices, engineering ports, and power supplies for control infrastructure. If panels are accessible without control, or ports are left exposed, cyber controls can be bypassed physically.
Relevant JBB services: Control Panels | Electrical Installations
Preventive measures: what to do now (without disrupting production)
The most effective approach is staged. Start by building visibility and reducing the easiest high-impact risks, then modernise where lifecycle risk is highest. The objective is continuous improvement without destabilising the plant.
Practical OT cyber improvement plan (engineering-led)
Step 1 - Baseline: map OT assets, remote access methods, and network zones. Establish a comprehensive asset inventory and implement continuous monitoring to provide real-time visibility, threat detection, and anomaly identification.
Step 2 - Stabilise: remove unknown connections, lock down shared credentials, document ownership
Step 3 - Segment: create controlled pathways and reduce lateral movement risk
Step 4 - Recoverability: implement versioned backups and prove restore
Step 5 - Modernise: address obsolete PLC/SCADA platforms and unsupported devices
Step 6 - Operate: embed change control, maintenance, and incident playbooks. Use exposure management to prioritise remediation efforts.
Preventive maintenance also plays a role in OT security because it enforces discipline: inspections, documentation updates, controlled changes, and condition-led interventions reduce the “unknown unknowns” that attackers exploit - and that engineers struggle with during incidents.
Relevant JBB service: Preventive Maintenance
How modern systems improve reliability (and security) together
Modernising OT is not just replacing hardware. It is an opportunity to rebuild reliability with security designed in. Modern architectures tend to improve uptime because they provide better fault visibility, better recovery, and clearer ownership - and those same characteristics reduce cyber exposure.
✅ What “good” looks like: A site where OT changes are controlled, remote access is governed, backups are proven, and network pathways are intentional - so both breakdowns and incidents are contained and recoverable.
Where JBB fits: OT risk reduction that respects operations
JBB Electrical supports industrial sites where uptime, compliance, and risk prevention are non-negotiable. OT cyber resilience is most effective when it is engineered alongside electrical infrastructure, control panel design, PLC/SCADA development, and maintenance strategy - not bolted on afterwards.
JBB Method: Assess → Modernise → Protect → Prevent → Support
Assess: establish OT visibility, identify remote access risk, and map critical dependencies
Modernise: upgrade obsolete control platforms and panel architectures that create single points of failure
Protect: implement segmentation, controlled access, and reliable monitoring
Prevent: embed disciplined maintenance, documented change control, and tested recovery
Support: provide ongoing engineering support to keep systems stable, secure, and audit-ready
Relevant JBB service: PLC Software
Book a Compliance & Breakdown Prevention Assessment
If your site relies on PLCs, SCADA, remote monitoring, or vendor access, cyber resilience is now part of operational risk management - and 2026/27 regulatory expectations are accelerating that reality. JBB’s Compliance & Breakdown Prevention Assessment identifies OT vulnerabilities that drive downtime exposure and compliance risk, then provides a practical, engineering-led improvement roadmap that respects uptime constraints.
Request a Compliance & Breakdown Prevention Assessment to reduce cyber-driven downtime risk, strengthen audit readiness, and improve control integrity across your industrial systems.
FAQs: Cyber security risks for industrial control systems (2026/27 regulations)
What risks does this issue create?
ICS cyber risk can cause unplanned shutdowns, loss of process visibility, compromised control integrity, and extended downtime during recovery. Insider threats pose a significant risk to industrial control systems, as trusted employees or contractors can exploit access to sabotage operations or steal sensitive data. Malware attacks on industrial control systems can damage physical equipment, leading to costly repairs.
What preventive measures should be taken?
Start with visibility: asset inventories, network diagrams, and a full remote access register. Then reduce high-impact risk through segmentation, controlled remote access with logging, and tested backup and restore. Use intrusion detection systems to monitor network traffic and detect suspicious activity within your industrial control environment.